Hey everybody,
This is yet another author’s writeup for BSidesSF CTF challenges! This one will focus on three crypto challenges I wrote: mainframe, mixer, and decrypto!
Continue readingHey everybody,
This is yet another author’s writeup for BSidesSF CTF challenges! This one will focus on three crypto challenges I wrote: mainframe, mixer, and decrypto!
Continue readingA long time ago, I wrote a couple blogs that went into a lot of detail on how to use padding oracle vulnerabilities to decrypt an encrypted string of data. It’s pretty important to understand to use a padding oracle vulnerability for decryption before reading this, so I’d suggest going there for a refresher.
When I wrote that blog and the Poracle tool originally, I didn’t actually know how to encrypt arbitrary data using a padding oracle. I was vaguely aware that it was possible, but I hadn’t really thought about it. But recently, I decided to figure out how it works. I thought and thought, and finally came up with this technique that seems to work. I also implemented it in Poracle in commit a5cfad76ad.
Continue readingGreetings, and I hope you’re all having a great holiday!
My Christmas present to you, the community, is dnscat2 version 0.05!
Some of you will remember that I recently gave a talk at the SANS Hackfest Summit. At the talk, I mentioned some ideas for future plans. That’s when Ed jumped on the stage and took a survey: which feature did the audience want most?
The winner? Tunneling TCP via a dnscat. So now you have it! Tunneling: Phase 1. :)
Continue readingHey everybody,
Live from the SANS Pentest Summit, I’m excited to announce the latest beta release of dnscat2: 0.04! Besides some minor cleanups and UI improvements, there is one serious improvement: all dnscat2 sessions are now encrypted by default!
Read on for some user information, then some implementation details for those who are interested! For all the REALLY gory information, check out the protocol doc!
Continue readingIt’s no secret that I love DNS. It’s an awesome protocol. It’s easy to understand and easy to implement. It’s also easy to get dangerously wrong, but that’s a story for last weeka few weeks ago. :)
I want to talk about interesting implication of DNS’s design decisions that benefit us, as penetration testers. It’s difficult to describe these decisions as good or bad, it’s just what we have to work with.
What I DON’T want to talk about today is DNS poisoning or spoofing, or similar vulnerabilities. While cool, it generally requires the attacker to take advantage of poorly configured or vulnerable DNS servers.
Technically, I’m also releasing a tool I wrote a couple weeks ago: dnslogger.rb that replaces an old tool I wrote a million years ago.
Continue readingIf you know me, you know that I love DNS. I’m not exactly sure how that happened, but I suspect that Ed Skoudis is at least partly to blame.
Anyway, a project came up to evaluate dnsmasq, and being a DNS server - and a key piece of Internet infrastructure - I thought it would be fun! And it was! By fuzzing in a somewhat creative way, I found a really cool vulnerability that’s almost certainly exploitable (though I haven’t proven that for reasons that’ll become apparent later).
Although I started writing an exploit, I didn’t finish it. I think it’s almost certainly exploitable, so if you have some free time and you want to learn about exploit development, it’s worthwhile having a look! Here’s a link to the actual distribution of a vulnerable version, and I’ll discuss the work I’ve done so far at the end of this post.
You can also download my branch, which is similar to the vulnerable version (branched from it), the only difference is that it contains a bunch of fuzzing instrumentation and debug output around parsing names.
Continue readingAs I promised during my 2014 Derbycon talk (amongst other places), this is an initial release of my complete re-write/re-design of the dnscat service / protocol. It’s now a standalone tool instead of being bundled with nbtool, among other changes. :)
I’d love to have people testing it, and getting feedback is super important to me! Even if you don’t try this version, hearing that you’re excited for a full release would be awesome. The more people excited for this, the more I’m encouraged to work on it! In case you don’t know it, my email address is listed below in a couple places.
Continue readingAs many of you know, last weekend was Ghost in the Shellcode 2015! There were plenty of fun challenges, and as always I had a great time competing! This will be my first of four writeups, and will be pretty simple (since it simply required me to use a tool that already exists (and that I wrote :) ))
The level was called “knockers”. It’s a simple python script that listens on an IPv6 UDP port and, if it gets an appropriately signed request, opens one or more other ports. The specific challenge gave you a signed token to open port 80, and challenged you to open up port 7175. The service itself listened on port 8008 (“BOOB”, to go with the “knockers” name :) ).
You can download the original level here (Python).
Continue readingHey folks,
I know in my last blog I promised to do a couple exploit ones instead of doing boring Web stuff. But, this level was really easy and I still wanted to do a writeup, so you’re just going to have to wait a little while longer for my ‘kappa’ writeup!
Continue readingHey folks,
This is my writeup for Whatscat, just about the easiest 300-point Web level I’ve ever solved! I wouldn’t normally do a writeup about a level like this, but much like the mtpox level I actually wrote the exact tool for exploiting this, and even wrote a blog post about it almost exactly 4 years ago - April of 2010. Unlike mtpox, this tool isn’t the least bit popular, but it sure made my life easy!
Continue readingHey folks,
This is going to be my first of a couple writeups about this past weekend’s CTF: PlaidCTF!
My first writeup is for a 150-point Web level called mtpox. I chose this one to do first not only because it’s the first level I completed, but also because the primary vulnerability was a hash extension issue, and I wrote one of most popular tools for exploiting those. So it’s like the level made for me!
(Actually, there’s another level that I wrote a less popular tool for. I’ll talk about that one in my next post. :) )
Continue readingThis post is about padding oracle vulnerabilities and the tool for attacking them - “Poracle” I’m officially releasing right now. You can grab the Poracle tool on Github!
At my previous job — Tenable Network Security — one of the first tasks I ever had was to write a vulnerability check for MS10-070 — a padding oracle vulnerability in ASP.net. It’s an interesting use of a padding oracle vulnerability, since it leads to code execution, but this blog is going to be a more general overview of padding oracles. When I needed to test this vuln, I couldn’t find a good writeup on how they work. The descriptions I did find were very technical and academic, which I’m no good at. In fact, when it comes to reading academic papers, I’m clueless and easily frightened. But, I struggled through them, and now I’m gonna give you a writeup that even I’d be able to understand!
By the way, the Wikipedia page for this attack isn’t very good. If somebody wants to summarize my blog and make it into a Wikipedia page, there’s now a source you can reference. :)
On a related note, I’m gonna be speaking at Shmoocon in February: “Crypto: You’re doing it wrong”. Among other things, I plan to talk about padding oracles and hash extension attacks — I’m really getting into this crypto thing!
Continue readingYou can grab the hash_extender tool on Github!
(Administrative note: I'm no longer at Tenable! I left on good terms, and now I'm a consultant at Leviathan Security Group. Feel free to contact me if you need more information!)
Awhile back, my friend @mogigoma and I were doing a capture-the-flag contest at https://stripe-ctf.com. One of the levels of the contest required us to perform a hash length extension attack. I had never even heard of the attack at the time, and after some reading I realized that not only is it a super cool (and conceptually easy!) attack to perform, there is also a total lack of good tools for performing said attack! After hours of adding the wrong number of null bytes or incorrectly adding length values, I vowed to write a tool to make this easy for myself and anybody else who's trying to do it. So, after a couple weeks of work, here it is!
Continue readingHey everybody!
While I was doing a pentest last month, I discovered an attack I didn’t previously know, and I thought I’d share it. This may be a Christopher Columbus moment - discovering something that millions of people already knew about - but I found it pretty cool so now you get to hear about it!
One of the first things I do when I’m looking at a Web app - and it’s okay to make a lot of noise - is run the http-enum.nse Nmap script. This script uses the http-fingerprints.lua file to find any common folders on a system (basically brute-force browsing). I’m used to seeing admin folders, tmp folders, and all kinds of other interesting stuff, but one folder in particular caught my eye this time - /.git.
Continue readingHey,
In my last post, I showed how we could guess the output of a password-reset function with a million states. While doing research for that, I stumbled across some software that had a mere 16,000 states. I will show how to fully compromise this software package remotely using the password reset.
Continue readingGreetings, all!
This is part one of a two-part blog on password resets. For anybody who saw my talk (or watched the video) from Winnipeg Code Camp, some of this will be old news (but hopefully still interesting!)
For this first part, I’m going to take a closer look at some very common (and very flawed) code that I’ve seen in on a major “snippit” site and contained in at least 5-6 different applications (out of 20 or so that I reviewed). The second blog will focus on a single application that does something much worse.
Continue readingHey everybody,
Most of you have probably heard of the exim vulnerability this week. It has potential to be a nasty one, and my brain is stuffed with its inner workings right now so I want to post before I explode!
First off, if you’re concerned that you might have vulnerable hosts, I wrote a plugin for Nessus to help you find them (I’m not sure if it’s in the ProfessionalFeed yet - if it isn’t, it will be soon). There’s no Nmap script yet, but my sources tell me that it’s in progress (keep an eye on my Twitter account for updates on that).
Continue readingLast year (if this intro doesn’t work, I give up trying to post this :) ), I presented at B-Sides Ottawa, which was put on by Andrew Hay and others (and sorry I waited so long before posting this… I kept revising it and not publishing). I got to give a well received talk, meet a lot of great folks, see Ottawa for the first time, and learn that I am a good solid Security D-lister. w00t!
Before I talk about the fun part, where I completely faked out my demo, if you want the slides you can grab them here: http://svn.skullsecurity.org:81/ron/security/2010-11-bsides-ottawa/. You can find more info about the conference and people’s slides at the official site. And finally, here’s a picture of me trying to look casual.
B-sides conferences, for those of you who don’t know, are awesome little conferences that often (but not always) piggyback on other conferences. They are free (or cheap), run by volunteers, and have raw and technical talks. B-sides Ottawa was no exception, and I’m thrilled I had the chance to not only see it, but take part in it. I really hope to run our own B-sides Winnipeg next year!
Continue readingHey all,
This is partly an overview of a new Nmap feature that I’m excited about, but is mostly a call to arms. I don’t have access to enterprise apps anymore, and I’m hoping you can all help me out by submitting fingerprints! Read on for more.
Continue readingHey all,
I just released the second alpha build of nbtool (0.05alpha2), and I’m hoping to get a few testers to give me some feedback before I release 0.05 proper. I’m pretty happy with the 0.05 release, but it’s easy for me to miss things as the developer.
I’m hoping for people to test:
Hey all,
We hired a new pair of co-op students recently. They’re both in their last academic terms, and are looking for a good challenge and to learn a lot. So, for a challenge, I set up a scenario that forced them to use a series of netcat relays to compromise a target host and bring a meterpreter session back. Here is what the network looked like:
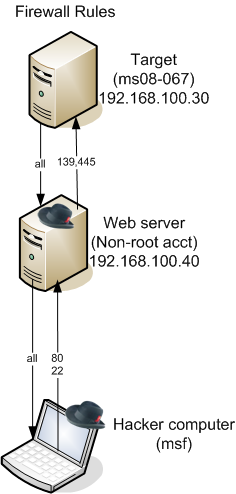 To describe in text:
To describe in text:
The challenge was to exploit the target server with ms08-067 and bring a meterpreter session back to the attacker server.
Continue readingThis post was written by Matt Gardenghi
This is just initial impressions of a beta product.
I’ve been playing with this for about a week now in an internal network. I have a dedicated box running Ubuntu 10.04 and Metasploit Express. I’ve noticed that Express loves CPU time but is much less caring about RAM. It’s also not multi-threaded. I’d recommend a dual core box as Express will peg one core. If you want to do anything else while Express is running, you need two cores. Still, Express does not require an expensive RAM build out. I’ve run top plenty of times and seen that the RAM usage remains low even when I’ve had 170+ shells running. :-p Hopefully, we’ll get multi-threading down the road. When multiple tasks are running simultaneously, this lack of multi-threading becomes an issue. Everything slows to a crawl.
Continue readingGreetings!
Today seemed like a fun day to write about a really cool vector for cross-site scripting I found. In my testing, this attack is pretty specific and, in some ways, useless, but I strongly suspect that, with resources I don’t have access to, this can trigger stored cross-site scripting in some pretty nasty places. But I’ll get to that!
Interestingly enough, between the time that I wrote this blog/tool and published it, nCircle researchers have said almost the same thing (paper (pdf)). The major difference is, I released a tool to do it and demonstrate actual examples.
Continue readingHey all,
I’ve been letting other projects slip these last couple weeks because I was excited about converting dnscat into shellcode (or “weaponizing dnscat”, as I enjoy saying). Even though I got into the security field with reverse engineering and writing hacks for games, I have never written more than a couple lines of x86 at a time, nor have I ever written shellcode, so this was an awesome learning experience. Most people start by writing shellcode that spawns a local shell; I decided to start with shellcode that implements a dnscat client in under 1024 bytes (for both Linux and Windows). Like I always say, go big or go home!
Continue readingHey all,
I’m really excited to announce the first release of a tool I’ve put a lot of hard work into: dnscat.
It’s being released, along with a bunch of other tools that I’ll be blogging about, as part of nbtool 0.04.
Continue readingGreetings everybody!
I spent a good part of the past month traveling, which meant staying in several hotels, both planned and unplanned. There’s nothing like having a canceled flight and spending a boring night in San Francisco! But hey, why be bored when you have a packet sniffer installed? :)
Continue readingHi all,
I wrote a blog last week about scanning for Microsoft FTP with Nmap. In some situations the script I linked to wouldn’t work, so I gave it an overhaul and it should work nicely now.
Continue readingGreetings!
I found this excellent writeup of a Web-server botnet on Slashdot this weekend. Since it sounded like just the thing for Nmap to detect, I wrote a quick script!
Continue readingHello once again!
I just finished updating my smb-check-vulns.nse Nmap script to check for the recent SMBv2 vulnerability, which had a proof-of-concept posted on full-disclosure.
WARNING: This script will cause vulnerable systems to bluescreen and restart. Do NOT run this in a production environment, unless you like angry phonecalls. You have been warned!
Continue readingHi all,
It’s been awhile since my last post, but don’t worry! I have a few lined up, particularly about scanning HTTP servers with Nmap. More on that soon!
In the meantime, I wanted to direct your attention to <a href=’http://blog.rootshell.be/2009/09/01/detecting-vulnerable-iis-ftp-hosts-using-nmap/’‘>This post (update here) about finding potentially vulnerable Microsoft FTP servers.
Continue readingI’m just going to quote my Slashdot post inline.. check out the links for all the nitty gritty details. The bottom line is that 5.00 is awesome, and includes everything I’ve written as yet – download it! :)
Continue readingHey all,
With the upcoming release of Nmap 4.85, Brandon Enright posted some comments on random Nmap thoughts. One of the things he pointed out was that people hadn’t heard of nbstat.nse! Since I love showing off what I write, this blog was in order.
Continue readingAhoy! My name is Andrew and I’ve been playing with the recent IIS WebDAV authentication bypass vulnerability (CVE-2009-1676) and helping Ron with writing the nmap detection script (http-iis-webdav-vuln.nse) and testing it in the lab. Ron is in a meeting today so I thought I’d jump in where he left off and post a bit about how to detect if WebDAV is enabled and how to actually exploit a folder once you’ve determined it is vulnerable.
Continue readingGreetings!
This morning I heard (from the security-basics mailing list, of all places) that there’s a zero-day vulnerability going around for WebDAV on Windows 2003. I always like a good vulnerability early in the week, so I decided to write an Nmap script to find it!
Continue readingI performed all of this to learn more about data exfiltration, remote control, etc… over a tightly controlled corp environment. It was depressing actually…. It’s far too easy to gain control of a corp network even one that is conscientious. This work is built on the info at metasploit.com.
Oh, let me just say thanks for Metasploit. Words fail to describe how nice this project is. Thanks guys.
So, I want to share what I’ve learned and offer some thoughts for pondering.
Continue readingIn case you haven’t heard, Fyodor released Nmap 4.85beta9 this week. This is the first release in awhile that wasn’t related to my code (or, most properly, mistakes :) ). It looks like the new stable version will be here soon, so give this one a shot and report your bugs. Here’s the download page.
Continue readingHi everybody,
With the help of Symantec’s Security Intelligence Analysis Team, I’ve put together a script that’ll detect Conficker (.C and up) based on its peer to peer ports. The script is called p2p-conficker.nse, and automatically runs against any Windows system when scripts are being used:
nmap --script p2p-conficker,smb-os-discovery,smb-check-vulns \
--script-args=safe=1 -T4 -p445 <host>
or
sudo nmap -sU -sS --script p2p-conficker,smb-os-discovery,smb-check-vulns \
--script-args=safe=1 -T4 -p U:137,T:139 <host>
See below for more information!
Or, if you just want to scan your network fast, give this a shot:
nmap -p139,445 --script p2p-conficker,smb-os-discovery,smb-check-vulns \
--script-args=checkconficker=1,safe=1 -T4 <host>
Continue reading
I’m going to start off this blog by wishing a happy birthday to a very important person – me. :)
Now, onto the content!
PsTools is a suite of tools developed by Sysinternals (now Microsoft). They’re a great complement to any pen test, and many of my Nmap scripts are loosely based on them. As good as they are, they aren’t without their quirks!
Here are a few topics worth discussing:
Most (possibly all) of the PsTools use standard Windows functions. That makes life easy – we can expect PsTools to act the same way other remote functions work. If we know how!
Continue readingAll right, maybe 0.02 doesn’t sound so impressive, but I’ve put a lot of work into it so eh?
Anyway, I just finished putting together nbtool 0.02. It is partly a test program for myself, and partly a handy tool for probing NetBIOS networks. Here is a link to the tool itself (I’ve tested this on Linux, OS X (ppc + intel), iPhones, and Windows (cygwin)): http://www.skullsecurity.org/wiki/index.php/Nbtool
Continue reading